Blogs
Read our latest blog for insightful tips and knowledge!
Filter by
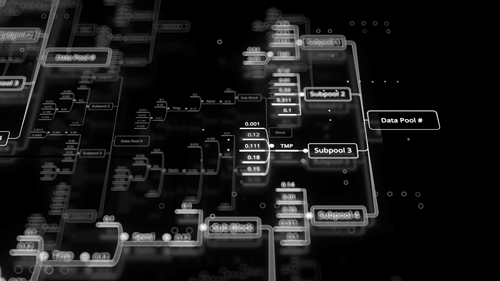
The Benefits of Network Functions Visualization
Software development teams, network operators and service providers all benefit from using Network Functions Visualization…

Container Security: Comprehensive Analysis vs. Specialty Analyzers
Securing a container involves analyzing for a variety of potential risks over a variety of…
Creating Effective Docker Images with the Help of Container Security
There are times Docker images are created without much thought to security. However, given the…
The Importance of Infrastructure as Code Analysis (IaC) in Container Security
When it comes to container security, many organizations focus on the host server or cluster.…
How Damaging Container Malwares Can Be
These malicious files can go undetected by many security solutions, and once they're inside your…

Docker Security Vulnerabilities That You Must Pay Attention To
Docker is a powerful tool that can help you increase the security of your containers…

How Container Security Refines DevOps Practices
In the ever-evolving software development landscape, the symbiotic relationship between DevOps and containerization has revolutionized…

Enforcing Reliable and Protected URL Encoding and Decoding in Java
Ensuring the security and integrity of data is paramount in the dynamic world of software…

Understanding SBOM: Enhancing Software Security and Transparency
Software plays a vital role in our daily lives, powering everything from smartphones to critical…
Safeguarding Your Data: Choosing the Right Architecture to Prevent Data Loss
Businesses and organizations rely heavily on the seamless information flow to make critical decisions, optimize…
