Blogs
Read our latest blog for insightful tips and knowledge!
Filter by
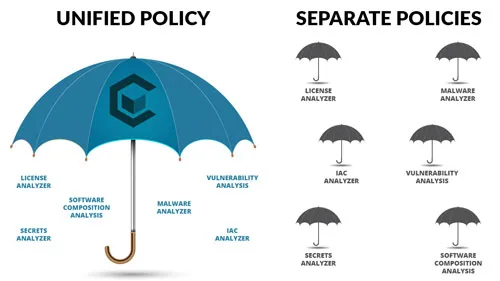
Choosing the Right Security Policy Solution
Security policies are a critical component of your security solution and selecting the right security…
Enhancing Container Security with Carbonetes - Lite App: A Comprehensive Overview
Container security plays a crucial role in safeguarding sensitive data and preventing potential vulnerabilities in…

The Importance of Container Host in Maintaining Security in Containerized Processes
Container security is an essential aspect of maintaining an effective containerized process. A container host…

How Your Business’s App Can Benefit From Having Container Security Management
As the world increasingly moves towards a digital landscape, more and more businesses are turning…
Why BOM Diggity is the Superior Container Security Platform
In an era where software security is a top concern, organizations must prioritize measures to…

The Best Docker Alternatives That You Should Check Out!
Docker is not the only containerization tool out there. In fact, there are several great…
The Challenges in Container Security That Can Be Overlooked
Container security is becoming increasingly important in the world of cloud computing. As containers become…
The Benefits of Network Functions Visualization
Software development teams, network operators and service providers all benefit from using Network Functions Visualization…
The Importance of Dependency Injection
Developers of the modern tech landscape are familiar with the concept of dependency injection and…

The Advantages of Containers Over Virtual Machines
Virtual machines changed the way IT departments delivered services, significantly increasing the speed and efficiency…
