Blogs
Read our latest blog for insightful tips and knowledge!
Filter by
Can AI Improve Code Security in DevOps? Exploring the Role of AI in Writing Secure Code
DevOps is a set of practices that combines software development and IT operations to enable…
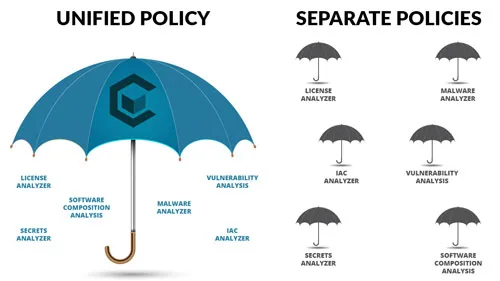
Choosing the Right Security Policy Solution
Security policies are a critical component of your security solution and selecting the right security…

Why Container Security Experts Are Necessary
As the world moves more of its infrastructure and applications to container platforms like Docker,…

The Advantages of Cloud-Native Security in Building Secure Applications
From computing down to data storage, cloud-native security is quickly becoming the preferred choice for…
The Importance of Infrastructure as Code Analysis (IaC) in Container Security
When it comes to container security, many organizations focus on the host server or cluster.…
Why BOM Diggity is the Superior Container Security Platform
In an era where software security is a top concern, organizations must prioritize measures to…
The Importance of Application Security Automation
In the age of digital transformation, application security is a critical concern for enterprises. The…

8 Tips on Securing Your Codes and Its Dependencies Properly
Containerization has emerged as an effective way to secure your code and its dependencies. It’s…

The Most Common Container Security Mistakes That You Must Avoid This 2023
New attacks might be lurking in the new year, but security professionals and IT leaders…

How to Prevent Supply Chain Attacks in 2023
When malicious actors target a company's supply chain, the consequences can devastate both the customer…
