Blogs
Read our latest blog for insightful tips and knowledge!
Filter by
Enhancing Container Security with Carbonetes - Lite App: A Comprehensive Overview
Container security plays a crucial role in safeguarding sensitive data and preventing potential vulnerabilities in…
Safeguarding Your Data: Choosing the Right Architecture to Prevent Data Loss
Businesses and organizations rely heavily on the seamless information flow to make critical decisions, optimize…
The Challenges in Container Security That Can Be Overlooked
Container security is becoming increasingly important in the world of cloud computing. As containers become…
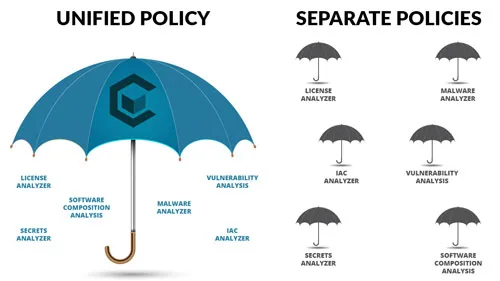
Choosing the Right Security Policy Solution
Security policies are a critical component of your security solution and selecting the right security…

5 Ways to Improve Container Security in Your DevOps Pipeline
As DevOps has become a popular approach to software development, containerization has become an essential…

Using IaC to Manage Edge Computing Infrastructure
Edge computing is the distribution of computing power and data storage closer to where data…

Safeguarding Your Code: A Comprehensive Guide to Penetration Testing Tools for Development Security
With sensitive data and valuable information being stored and processed within applications, ensuring development security…
Enhancing Container Security with Carbonetes - Lite App: A Comprehensive Overview
Container security plays a crucial role in safeguarding sensitive data and preventing potential vulnerabilities in…
Why BOM Diggity is the Superior Container Security Platform
In an era where software security is a top concern, organizations must prioritize measures to…

Enhancing Cloud Security Like No Other with BrainIAC
In the dynamic landscape of cloud computing, security remains a paramount concern. As organizations increasingly…
