Blogs
Read our latest blog for insightful tips and knowledge!
Filter by
How Threats Can Easily Infiltrate Containerized Applications
Containerized applications are very vulnerable to threats even when they are not running. Here's how…
How Cloud Scanning Revolutionized Container Security
Cloud Scanning has become an essential component of any business' cybersecurity arsenal. Here's how it…

Container Security: Comprehensive Analysis vs. Specialty Analyzers
Securing a container involves analyzing for a variety of potential risks over a variety of…
Keeping Your Docker Secrets a Well-Kept Secret
Docker Secrets are config files that contain sensitive information, like passwords, tokens, and keys. Unlike…
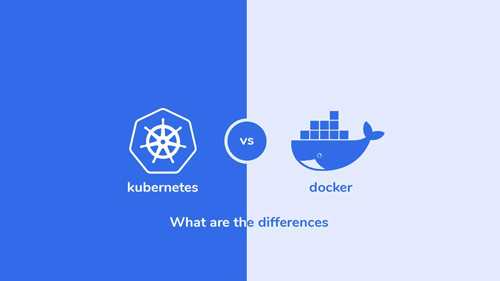
Docker vs. Kubernetes: What Are the Differences
When it comes to container orchestration, two powerful tools stand out: Docker and Kubernetes. Both…

The Most Common Container Security Mistakes That You Must Avoid This 2023
New attacks might be lurking in the new year, but security professionals and IT leaders…
Can AI Improve Code Security in DevOps? Exploring the Role of AI in Writing Secure Code
DevOps is a set of practices that combines software development and IT operations to enable…

Containerization and Microservices: The Future of DevOps
Technology advances and evolves, so do the approaches and methodologies in software development. One of…

Containerized Deployment Strategies for DevOps Teams
Containerization is changing the way that DevOps teams approach application deployment. By providing a portable,…

5 Ways to Improve Container Security in Your DevOps Pipeline
As DevOps has become a popular approach to software development, containerization has become an essential…
