Blogs
Read our latest blog for insightful tips and knowledge!
Filter by

Containerization and Microservices: The Future of DevOps
Technology advances and evolves, so do the approaches and methodologies in software development. One of…

5 Ways to Improve Container Security in Your DevOps Pipeline
As DevOps has become a popular approach to software development, containerization has become an essential…
The Importance of Application Security Automation
In the age of digital transformation, application security is a critical concern for enterprises. The…

The Importance of SBOMs in Managing IoT Software Security
Building with open-source software is essential for many IoT developers. Open-source software provides a wealth…
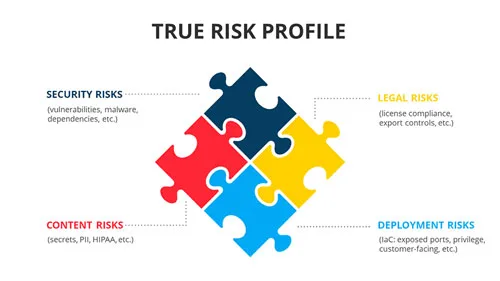
Container Security Asset Management
Container security is the practice of correlating all inherent security risks in conjunction with the…
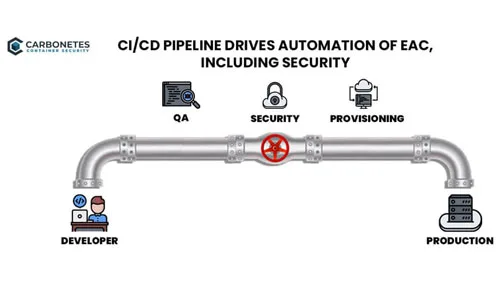
Security & CI/CD Toolchains
Modern security tools provide a variety of implementation options including full-function clients, APIs and CI/CD…

The Human Factor in Container Security: Unlocking the Power of Awareness and Training
Containerization has revolutionized software development and deployment, allowing faster and more efficient application delivery. However,…

How Container Security Platforms Help in the Aftermath of a Security Threat
In today's interconnected digital landscape, where security threats loom large, organizations continually seek robust solutions…

5 Effective Ways to Mitigate the Risk of Malicious Packages in Open Source Ecosystems
Open-source software has revolutionized how software is developed and distributed, providing access to a wealth…
5 Things AI Code Writing Can't Do in DevOps: Why Human Developers Remain Essential
Artificial intelligence (AI) has become an increasingly popular tool for automating repetitive tasks and increasing…
